Static Analysis
Code, Dependencies, Secrets, Infra as Code
Vulnerability scanning orchestration platform for confidential and comprehensive vulnerability management.
ScanSuite glues the best tools together enabling comprehensive vulnerability management on-premise or in the cloud.
Code, Dependencies, Secrets, Infra as Code
Quickly identify and assess vulnerabilities in web applications
Scan and assess the security of your external and internal perimeters
Enumeration of subdomains, hosts, websites, emails and leaked credentials
Fully automated OSINT for external attack surface mapping.

Vulnerability Scanning, Credentials Bruteforce, Authenticated Patching Checks, Docker Image Scans
Analyse both external and internal perimeters for active hosts, open ports, vulnerable serivces. Run bruteforcing attacks using leaked credentials and powerful wordlists. Ensure the servers patching level is up to date. Schedule scans. Analyse docker images for environmental vulnerabilities.

DAST, Fuzzing, API Scans, Hidden paths, CMS analysis
Scan running web applications for known vulnerabilities and 0-days. Run authenticated scans. Schedule scans for periodic analysis.

SAST, ML-SAST, SCA/OAST, IACS
Find vulnerabilities in source code, dependencies and configurations. Perform incremental code analysis, schedule periodic scans. Analyse code with local and cloud LLMs.

For Static, Web and Infrastructure Scanning
Scan with custom rules across all targets. Generate rules with AI.

Vulnerability Management System
View, track and remediate vulnerabilities. Create HTML/PDF/CSV reports. Process false positives and risk acceptance. Enable metrics, dashboards, benchmarks, SLA. Upload findings to Jira and track remediation progress.

Seemless integration with CI/CD products
Run security scans within your pipelines. Analyse results in Defect Dojo.

Having public exploits or noticed in malware campaigns.
The most complete database with known exploitable vulnerabilities. Auto checks during infrastructure and dependency scans.

Automated AI generation for code repositories
Generate the source code documentation with AI. Store and read it via convenient web interface.

Code analysis and documentation, Findings verification and endrichment, Rules generation and much more
Executed on thousands of services and codebases
Infrastructure and Web scans also supported
For custom Static, Web and Infrastrucutre scans
Map your attack surface before hackers do
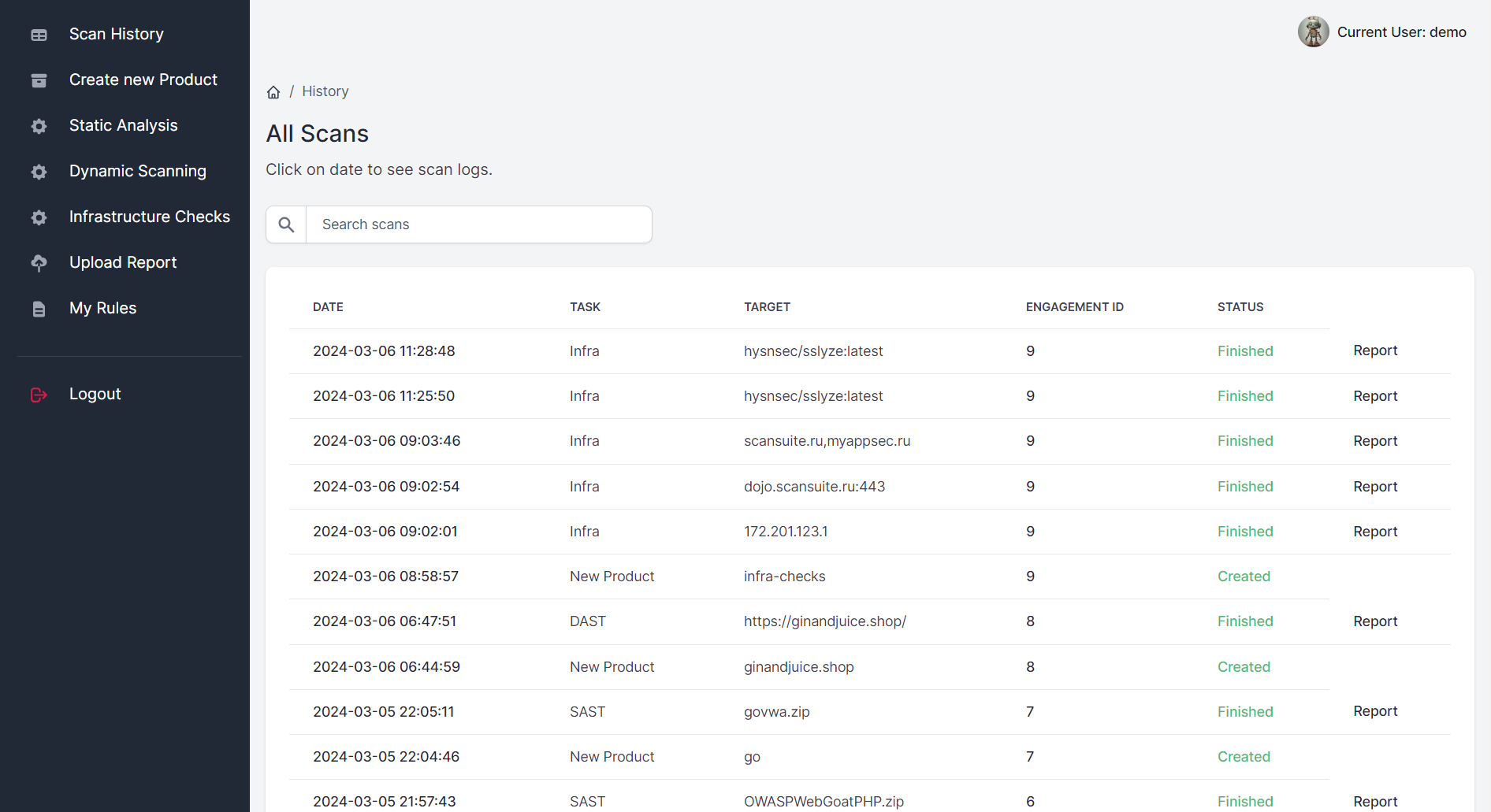
Vulnerability scanning and remediation
Feature rich vulnerability management
Best vulnerability scanners enabled
Development languages supported
Manage vulnerabilities locally or in secure cloud
Module to support continuous security
Database with auto verification and prioritesation of publicly known vulnerabilities.
IDE plugins, data classification, and engineering checklists catch risks before code leaves the developer workflow.